Alexander Hoffmann
Bio
Passionate cybersecurity expert with 15+ years securing corporate realms. Ethical hacker, password guardian. Committed to fortifying users' digital safety.
Stories (51)
Filter by community
Complete Guide: Legitimate Gmail Password Recovery & Account Security. AI-Generated.
Forgetting a Gmail password can be frustrating, but attempting to recover it through unauthorized means can lead to security risks and legal consequences. This comprehensive guide provides verified, legitimate methods for Gmail password recovery, explains common threats to account security, and offers actionable protection strategies. We strongly advise against using any "hacking software," as these are often scams or malware that compromise your privacy and violate Google's Terms of Service.
By Alexander Hoffmann2 months ago in 01
The Complete Guide to Recovering Your Snapchat Password (Legitimate Methods & Protection Tips). AI-Generated.
Losing access to your Snapchat account can be frustrating and concerning. Whether you've forgotten your password or suspect unauthorized access, this comprehensive guide provides legitimate recovery methods, essential protection strategies, and answers to frequently asked questions. It's crucial to emphasize that hacking into someone else's Snapchat account is illegal and unethical. This article focuses exclusively on legitimate account recovery for your own account and protective measures.
By Alexander Hoffmann2 months ago in 01
How to Recover Your Instagram Password: Ethical Methods and Security Guide. AI-Generated.
Losing access to your Instagram account is frustrating. Whether you've forgotten your password or suspect unauthorized access, this guide provides the most effective recovery methods currently available. We'll explore legitimate recovery options, review password security tools, and offer essential protection strategies. Important note: This article covers password recovery for your own account only. Unauthorized access to others' accounts violates Instagram's terms and may be illegal.
By Alexander Hoffmann2 months ago in 01
Complete Guide to Hack Snapchat Account Security in 2026: Threats, Protection & Recovery. AI-Generated.
Understanding Snapchat Security in the Modern Age Snapchat remains one of the world's most popular social platforms, with its ephemeral messages and stories creating a unique digital environment. However, this popularity makes it a target for malicious actors. Whether motivated by jealousy, curiosity, or malice, attempts to compromise Snapchat accounts are increasingly common. This comprehensive guide will explore the real methods used by attackers, introduce legitimate security testing tools used by professionals, and most importantly, provide a complete blueprint for protecting your account and recovering it if breached.
By Alexander Hoffmann2 months ago in 01
The Complete Guide to Wi-Fi Hacking: How Networks Are Compromised and How to Protect Yours. AI-Generated.
The Invisible Threat to Your Wireless Network In our hyper-connected world, Wi-Fi has become as essential as electricity. From smart homes to remote work, we depend on wireless networks for virtually everything. Yet, this convenience comes with significant risks. Wi-Fi hacking represents one of the most pervasive and potentially damaging cyber threats facing individuals and organizations today. Understanding how these attacks work isn't just technical knowledge—it's a necessary layer of digital self-defense in our increasingly wireless world.
By Alexander Hoffmann2 months ago in 01
The Ultimate Guide to Regaining Access to Your Instagram Account. AI-Generated.
Lost access to your Instagram account? Our comprehensive guide covers official recovery methods, security protocols, preventive measures, and answers to all your questions about restoring your Instagram presence.
By Alexander Hoffmann2 months ago in 01
The Real Methods of Gmail Hacking: How Accounts Are Compromised and How to Protect Yourself. AI-Generated.
The Illusion of Invulnerability A Gmail account is more than just an email inbox—it's a digital passport to our online identity, connecting our social media, financial services, cloud storage, and professional communications. Many users operate under the dangerous assumption that Google's security is impenetrable, but the reality is that human error and sophisticated attacks create vulnerabilities that hackers exploit daily. This comprehensive guide will explore the actual methods used to compromise Gmail accounts, examine the tools employed by malicious actors, and provide actionable strategies to fortify your digital presence against these threats.
By Alexander Hoffmann2 months ago in 01
The Real Methods of Outlook Hacking: How Accounts Are Compromised and How to Protect Yourself. AI-Generated.
Microsoft Outlook, with over 400 million active users, is a prime target for cybercriminals. This article isn't a guide to hacking; it's a forensic look at the real methods attackers use to compromise Outlook accounts. By understanding these techniques, you can build an impenetrable defense. We will delve into the dark underbelly of cyber threats, expose the tools used (for educational awareness only), and equip you with the knowledge to shield your digital life.
By Alexander Hoffmann2 months ago in 01
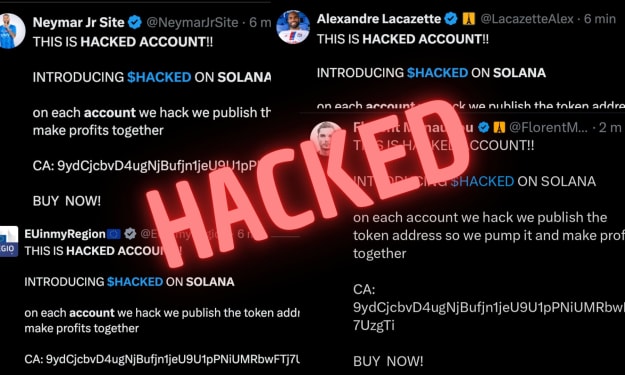
The Real Methods of Hacking: How X (Twitter) Accounts Are Hijacked and Fortified. AI-Generated.
When Your Digital Voice Gets Stolen Your X account isn't just a social profile—it's your public voice, professional network, and personal brand all rolled into one. Yet this visibility makes it a prime target for digital intruders. Beyond simple password guessing, today's attackers deploy sophisticated psychological and technical tactics that exploit both platform features and human nature. This guide exposes the actual breach methods threatening X accounts, details the protective measures that genuinely work, and provides a realistic roadmap to securing your social presence.
By Alexander Hoffmann2 months ago in Lifehack
Yahoo Account Hack 2026. AI-Generated.
As one of the oldest and most established email providers, Yahoo accounts represent attractive targets for cybercriminals due to their longevity and frequent connection to other online services. This comprehensive guide examines Yahoo account security through both defensive and analytical lenses, with the understanding that unauthorized account access violates laws and ethical boundaries globally.
By Alexander Hoffmann2 months ago in 01
The Complete Guide to Hack Facebook Account Security in 2026. AI-Generated.
Have you ever wondered how Facebook accounts are compromised, or more importantly, how you can shield yours from such an invasion? In an era where our digital and social lives are deeply intertwined, a hacked Facebook account can lead to more than just embarrassing posts—it can result in financial fraud, identity theft, and a profound loss of privacy. This guide delves into the mechanics behind Facebook hacking not to enable malicious activity, but to empower you with knowledge. By understanding the tools and techniques cybercriminals use, you can build an impenetrable defense for your online identity.
By Alexander Hoffmann2 months ago in 01
The Complete Guide to Hack X (Twitter) Account Security in 2026. AI-Generated.
With over 500 million monthly active users, X (formerly Twitter) has become a prime target for cybercriminals seeking to compromise accounts for financial gain, spreading misinformation, or identity theft. This comprehensive guide examines account security from both defensive and offensive perspectives for educational purposes, emphasizing that unauthorized access to accounts is illegal and unethical.
By Alexander Hoffmann2 months ago in 01