cybersecurity
Our personal, digital, national and military security depend on a safe cyber space.
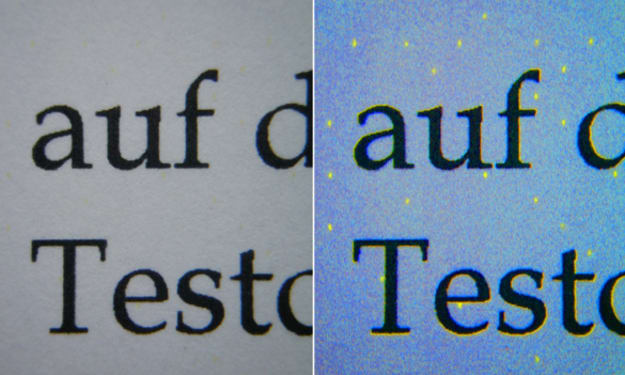
How Your Printer Is Snitching on You
Printers are one of the most commonly used computer peripherals essential to every home and office. But, did you know that these devices are also designed to sell you out? Every piece of paper that comes out of your printer contains more information than you know, slipped in there for the sole purpose of tracking your documents back to you.
By Jack Warner7 years ago in 01
The Dark Web
**This article contains mature/adult themes and topics and is may not be suitable for some readers. I am also absolutely not at all in any way condoning or promoting illegal activity of any kind. This article is purely for entertainment/informational purposes only.**
By Kamryn Davis7 years ago in 01
Are They Listening?
Technology is all around us, and the amount of technology we have in our home is increasing everyday. Many of these new technologies have raised some questions about privacy. Whether it be Alexa or our cell phones, numerous accounts suggest that they are listening to us. This is most likely not the first time you have heard this debate, but it recently happened to me first hand.
By Derek Mihalecsko7 years ago in 01
10 Ways to Keep Your Phone Safe from Theft
Last year, over 2 million Americans had their phones stolen. Phone thefts usually happen in public areas when your guard is down. Luckily, there are simple steps you can take to prevent this from happening, as well as precautions to put in place so that if it does get stolen, you have a better chance of tracking it. Be alert, be smart, and be intentional about living in a way that is ensured to keep your phone safe from theft.
By James Lizowski7 years ago in 01
Hounded on All Sides: Freedom in Digital Spaces
The pervasion of mental spaces has increased dramatically over the last decade, particularly with the rise of social media. Most digital spaces have been sold and bought by corporations who push their corporate messages consistently onto vulnerable users. Such users (but not all) are vulnerable because they enjoy these spaces to relax and thus are not sufficiently circumspect against hidden advertisement. These corporate messages infiltrate mental spaces at such a regular and constant pace that they become assimilated unconsciously by users, which Alyssa Loh emphasises with regard to the USA; “Democracy in the United States, however, is less likely to end in spectacular violence than in the banal chug of market force...the gravest threat to our freedom today may be the steady erosion of our spaces of mental freedom.”
By Harriet Weston7 years ago in 01
International Day of Older Persons: Top Tips to Keep Seniors Safe Online
On October 1st, the world celebrated the International Day of Older Persons. This international day was initiated by the United Nations. It is estimated that there are almost 700 million people over the age of 60 worldwide, and this number is rapidly growing every year.
By Laura Tyrell7 years ago in 01
Can We Make the Internet Great and Free Again?
Thirtysomethings can still remember the days when Internet meant open, secure, and neutral space to share, search, and communicate. It promised democracy, equality, and knowledge. A decade or two ago, user privacy meant being online with no one else peeking over your shoulder. But times have changed…
By Laura Tyrell7 years ago in 01
9 Keys for Password Protection. Top Story - September 2018.
Cyber crimes and threats to online public information are on the rise. With hackers all around the world finding new ways of getting inside your personal online zone, the need for safer mechanisms and novel ways of protecting information is on an all new high. Apart from safety programs that one can pay for enrolling in, there are some basic steps which each of us can take to ensure that our information is a little more secure. The first and most important step in this regard is protecting our passwords.
By Sukriti Taneja8 years ago in 01
Social Engineering: How Cyber Criminals Thrive on Human Psychology
Social engineering is becoming one of the most popular methods used by cybercriminals for both big and small crimes. Essentially, social engineering is a way to gain access to networks, systems, or data by exploiting human psychology and curiosity rather than using technical hacking techniques. Using a variety of methods, including phone calls and social media messaging, attackers trick people into giving them access to valuable personal or corporate information.
By Laura Tyrell8 years ago in 01
A Virginia Bank Breached Twice and No Fix
Hello folks, this is Jared once again, and this time, I’m here to talk about an article entitled "Hackers Breached Virginia Bank Twice in Eight Months, Stole $2.4M" and how I think its the bank that neglected to fix the underlying problem.
By Jared Rimer8 years ago in 01